With breach after breach making headlines today as well as various cybersecurity incidents being reported in unprecedented numbers, businesses today are having to rethink their security architecture. The security of environments includes considering how end users are able to access business-critical systems. Generally speaking, user access is assigned based on identity. Identity is the mechanism of validating that someone is who they say they are. Time and again, it is found that traditional means of securing resources is quickly becoming outdated and easily compromised by attackers. These security concerns are present across both full end user clients as well as VDI thin client devices. Why are traditional means of security simply not enough in today’s world of growing cybersecurity threats? How can organizations engineer simple and secure access to company resources and still ensure the security of systems and data? Let’s take a look at how Praim’s Smart Identity with Agile 2.6.1 is able to provide this simple and secure access to resources effectively and efficiently.
Why Traditional Identity is Failing Organizations
Establishing identity plays perhaps the most crucial part in security for end users accessing valuable company resources. Based on identity, users are granted permissions or assigned roles that determine their overall abilities to access files, folders, or other data stored. Attackers most often look for the “low hanging fruit” for security compromise. Often, this involves compromising user credentials to gain unauthorized access to sensitive or otherwise critical data. What do attackers often look for? Weak Passwords.
Traditional security involving the classic username and password is failing to secure today’s data. Many end users, including high-level access users with dangerous access permissions, are using weak passwords for their accounts. Why is this the case? Weak passwords are easy to remember. Humans are generally creatures of least resistance and effort. Many end users do not want the extra hassle of remembering a complex password and having to periodically change their password to yet another complex password. This leads end users to simply change a single character or add a different number to a very weak password that barely satisfies any complexity or password requirements.
These types of habits by end users creates a massive security vulnerability in the username and passwords themselves. Many users use easily guessable passwords that are common words found in a dictionary. Attackers sometimes use what is called “dictionary attacks” to gain access to systems by using automated tools to try hundreds or even thousands of passwords against a number of accounts to try to guess the password of end users. More often than not, they can find an account of a user who is using a very weak password that is easily “guessed” using one of these automated tools.
Other scams and tactics of attackers can also prove extremely fruitful. This includes phishing attacks that can trick end users into disclosing their credentials in some way. As basic and “old school” as the technique of phishing is, the technology presented to end users by way of websites and emails have gotten much more sophisticated and can easily pass as legitimate requests for information to the unsuspecting and untrained eye.
Strong Security Requires Multi-Factor Authentication
When looking at ways to bolster the security of “identity”, multi-factor and also smart card or similar authentication are tremendously powerful. With smart card authentication, you have a physical “token” such as a smart card that you possess which the user has to physically possess to login to their end user system. With multi-factor authentication, a user has to know a piece of information which is their password but they also have to physically possess the token that completes the chain of authentication required for accessing the system.
If an attacker steals the user’s credentials including their password, they still do not possess the full circle of security information needed to complete the authentication request as the true end user still possesses the physical token required for authentication.
Verifying identity applies as well with VDI technologies to allow users to gain access to the VDI infrastructure. Many organizations may shy away from configuring multi-factor or other smart token access due to the complexity of configuring the extra security.
Praim Smart Identity – Simple and Secure Access
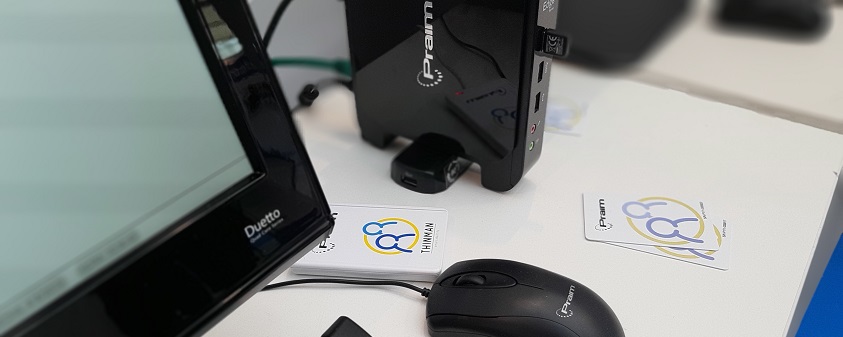
Praim’s Smart Identity solution works in harmony with Praim Agile to provide a simple, secure, and seamless solution for providing more secure access to VDI environments. It is designed to work with many smart cards and readers: both with physical reading of the card through insertion (contact), and with proximity card with NFC (contactless) technology. Smart Identity allows you to enable different types of access and security, in a granular way, with total control of both users and authentication methods used.
The enrollment process is totally under control of the administrator, who decides which devices could enroll the smart cards, how many cards a user can enable, as well as decide to block unwanted devices and smart cards.
Praim Smart Identity can be configured in two configurations for authenticating end users to VDI environments:
- Authentication Device
- Identification Device with Multi-Factor

Praim Smart Identity
When using Praim ThinMan Smart Identity as an authentication device, a smart physical device is used such as a smart card for authentication. In this configuration mode, there is no need for a password to be entered from the end user as the smart device takes care of the complete authentication mechanism. The workflow for the authentication process includes the following:
- Praim ThinMan Smart Identity validates whether the smart card is active
- User Access is granted to the device and its resources
- Device or user profiles are applied from ThinMan server
- When the user is finished, tapping the card or removing it from the reader will lock or log the session out from the device.

Using Praim ThinMan Smart Identity in the identification device mode, the smart card is used to identify the user, then a second-factor authentication mechanism such as a PIN or domain password is used to authenticate the user to the device. The authentication workflow for the end user in this mode includes the following:
- User presents the identification device
- Praim ThinMan server checks to see if the smart card is active and recognized
- If recognized, a second-factor authentication mechanism is prompted
- If the PIN or domain password is validated, the user session is granted access to the device and its resources
- ThinMan device and user profiles are applied
Organizations are looking for simple, yet secure technology solutions to solve the very complex and intricate challenges of today’s digital landscapes as indicated by Praim’s Chief Sales Officer, Stefano Bonmassar:
“The digitalization of processes must guarantee simplicity, transparency, but at the same time high security and service continuity, for this reason technological choices are very important.“
Recently, Praim released version 2.6.1 of Agile sporting the Smart Identity technology. Agile with Smart Identity has some really great new features to speak of in this release. This includes the new ability to pass credentials used to login to ThinMan to the Windows Credential Manager. Praim automates this process with the following:
- Credentials are stored in Windows Credential Manager
- These are automatically removed when the logoff process is initiated or when the smart card is removed
This gives IT administrators more flexibility with scripting and other mechanisms to mount network drives, network printers, or other devices using credentials passed on to Windows from ThinMan Server.
Concluding Thoughts
Praim’s Smart Identity solution is a simple and secure way to access resources. It allows companies to manage smart token devices and multi-factor access easily. By implementing the Smart Identity solution, businesses are able to transition from the legacy methods of username and passwords to the modern and more secure approach of token-based access to VDI environments.